Obtaining Certificates Automatically Using SCEP¶
| Setting | Default | AWI | OSD | Management Console |
|---|---|---|---|---|
| Certificate Usage | ||||
| SCEP Server URL | ||||
| Challenge Password | ||||
| CA Identifier | ||||
| Auto Renewal Period | 0 (disabled) | |||
| Issuing CA Certificate | ||||
| Client Certificate | ||||
| Request Certificates (button) | ||||
| Status |
You can simplify the retrieval and installation of digital certificates by enabling devices to obtain certificates automatically from a Simple Certificate Enrollment Protocol (SCEP) server.
You can obtain certificates using SCEP for:
-
802.1X: Allows you to use SCEP to automatically request a custom certificate to use in your 802.1X configuration.
Enabling 802.1X
Enabling 802.1X also requires enabling 802.1X in the Configuration > Networking page of the OSD or AWI.
-
Administrative Web Interface: Allows you to use SCEP to automatically request a custom certificate for connections to the Administrative Web Interface (AWI).
-
Peer-to-peer Max Compatibility: Allows you to use SCEP to automatically request a custom certificate that allows secure negotiation using any of the common cipher suites to offer flexibility for your network security requirements.
-
Peer-to-peer Suite B: Used in environments requiring Suite B cryptography. Allows you to use SCEP to automatically request a custom certificate offering the greatest security for negotiating session connections with a PCoIP endpoint.
SCEP Behaviors¶
The following behaviors are observed when using SCEP to obtain your certificates.
-
A successful SCEP request for a certificate will install the SCEP certificate in the endpoint's certificate store.
-
A successful SCEP request for a certificate will no longer store the Root CA (or issuing CA) certificate in the endpoint's certificate store.
-
The OSD and AWI SCEP tab will display the Subject and Issuer names of the SCEP client certificate.
-
Deleting a peer-to-peer certificate will cause it to revert to using the default peer-to-peer certificate. This will take effect on next session connection.
-
Deleting an AWI SCEP certificate will cause it to revert to using the default AWI certificate. A reboot is required.
-
Removing a 802.1X SCEP certificate happens immediately. The endpoint will fail 802.1X authentication on the next connection attempt or on the next automatic polling with the 802.1X switch.
-
Additional successful SCEP requests will overwrite any previously installed SCEP certificates for the same usage.
-
Endpoint SCEP certificate requests include the following parameters:
-
Subject Name: PCoIP Device Name
-
Subject Alt Name: MAC Address, User Principal Name (UPN), and the Fully Qualified Domain Name (FQDN)
-
-
SCEP certificate renewal requests occur sequentially in 1 hour intervals when the renewal setting has been reached. The first request must successfully complete before renewal of the next certificate is initiated. If unsuccessful, the renewal request for the first certificate is attempted again. Administrators should periodically review the validity period of the SCEP certificates to ensure that renewals were successful and the certificates do not expire.
-
The PCoIP endpoint must have NTP properly configured.
-
The renewal period must be less than the validity period of the certificate.
-
Based on the configured renewal setting, an endpoint will automatically issue a SCEP renewal request using the existing certificate for authentication
Using Microsoft NDES
Renewal using Microsoft NDES encounters a problem when the Certificate template is configured to populate the Subject Name with multiple attributes from Active Directory information (e.g. CN, OU, DC), such is the case when setting the Subject Name to Fully distinguished name.
To avoid this issue:- Set the Subject Name to be supplied in the request
- Set the Subject Name to be populated with just the Common Name from the Active Directory
-
Endpoint SCEP requests do not use a TLS connection. The Tera2 endpoint generates its own 3072-bit SCEP RSA private key when certificates other than Peer-to-peer Suite B certificates are requested. For Peer-to-peer Suite B certificates, the endpoint generates its own ECC P-384 SCEP private key.
The private key is used to construct parts of the PKCS#10-formatted certificate request which is then delivered to the SCEP server, and the SCEP server's Registration Authority (RA) RSA certificate's public key is used to encrypt the actual certificate request. The SCEP challenge password is encrypted as it is contained within the certificate request.
The following cryptography algorithms are used to generate a SCEP request:-
Content Key Encryption Algorithm: RSAES-OAEP
-
Hash Algorithm: SHA384
-
Content Encryption Algorithm: AES-256-CBC
-
Endpoint Session TLS Security Mode settings
Hardware endpoints have a required TLS Security Mode setting in each session configuration (i.e. AWI > Session). The SCEP request must correspond to the TLS Security Mode setting used on the endpoint.
-
If the selected TLS security mode is Suite B, only ECC certs can be selected using the Peer-to-Peer Certificate drop down list.
-
If the selected TLS security mode is Max compatibility, only RSA certs can be selected using the Peer-to-Peer Certificate drop down list.
-
The session TLS security mode must match the selected SCEP issued peer-to-peer certificate—Peer-to-peer Max Compatibility or Peer-to-peer Suite B—to establish a successful secure peer-to-peer connection.
If the endpoint is not configured with the correct session TLS Security Mode, the Peer-to-Peer Certificate field in the AWI Configuration > Session page will not change and remain as Default, even though the Upload > Certificate page shows the active SCEP issued certificate in the Selected Peer-to-Peer Certificate field. -
Peered endpoints will not connect until the TLS setting matches the type of certificate being used and the peered endpoint has the matching configuration.
The following settings display on the OSD and AWI SCEP pages:

OSD SCEP page
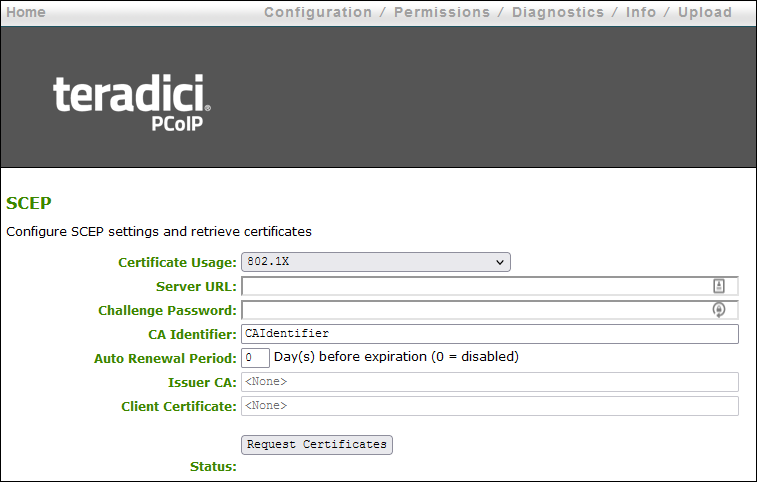
AWI SCEP page
SCEP Parameters
| Parameter | Description |
|---|---|
| Certificate Usage | There are 4 options:
|
| SCEP Server URL | Enter the URL for the SCEP server that is configured to issue certificates for the device. |
| Challenge Password | Enter the password required by the SCEP server |
| CA Identifier | A string provided by your CA issuer that uniquely identifies the Certificate Authority when providing certificates for SCEP requests. |
| Auto Renewal Period | Number of days prior to the existing certificate expiry date to initiate a certificate SCEP renewal request. If left unconfigured, administrators must manually request a new certificate. |
| Issuer CA Certificate | Displays the Issuer CA certificate that signed the client certificate. (The endpoint no longer stores the Root CA certificate) |
| Client Certificate | Displays the name of the client certificate that has been installed in the device. |
| Request Certificates (button) | After entering the SCEP server address, password, certificate usage, and CA Identifier, clicking this button initiates the retrieve certificates process. |
| Status | Displays the status of the request (for example, requesting, successful, failed). |
To obtain certificates automatically using SCEP:¶
-
Open the SCEP page:
- From the OSD, select Options > Configuration > SCEP.
- From the AWI, select Configuration > SCEP.
-
Select the Certificate Usage type.
Using Peer-to-peer certificates
If using a Peer-to-peer certificate, confirm the TLS Security Mode in the advanced section of your Session connection matches your certificate type. A successful secure connection can only happen when the corresponding PCoIP endpoint has the correctly configured certificate applied. See Peering Zero Clients to Remote Workstation Cards
-
Enter the URL and challenge password for the SCEP server.
-
Enter the CA Identifier if required. Provide a valid CA Identifier or use "CAIdentifier" (default).
-
Enter the Auto Renewal Period.
-
Click Request Certificates to retrieve the certificate. The issuing CA and client certificates display after a successful SCEP request.
The Status section displays the status of the request such as Requesting, Request completed, or Request failed. Once the SCEP process is completed, the certificate is active.
To delete your SCEP certificate:¶
-
Browse to the AWI Upload > Certificates page.
-
Click the Remove button beside the certificate you wish to remove.
-
Click Apply and then Continue.